jBPM 5 application using a simple Hello World project in combination with the Eclipse
jBPM plugin.
jBPM 5 can be freely downloaded from sourceforge here. jBPM 5 is basically distributed in two formats: the
jbpm-5.X.X.Final-installer-full.zip
which includes really lots of stuff (including the core libraries, the
JBoss AS, the Eclipse plugins and the Web application consoles) and the
jbpm-5.X.X.Final-bin.zip which contains just the jBPM 5 libraries and thus it's good for distributing it in production.
For
the purpose of learning we will download the latest
jbpm-5.X.X.Final-installer-full.zip which contains all the stuff needed
to learn jBPM. Once downloaded unzip the package in a folder of your
preference.
You need to have Jakarta ant installed in order to continue
Ok now you can get started in two ways:
1# Option: Installing all the components contained in the package using:
ant install.demo
2# Option: If you want to install the component step
by step you will understand better the role of every single component
of jBPM 5. Here's how to do it:
You need to have Eclipse Indigo installed in order to continueNow open the file
build.properties which is used by ant and specify the path where Eclipse is installed:
For example, if you have installed Eclipse into C:\
# the home of your eclipse installation will be
# used to deploy the Eclipse plugin to
eclipse.home=C:\\eclipse
Ok, now we will install the jBPM Eclipse plugin with the following ant command:
ant install.droolsjbpm-eclipse.into.eclipse
And then we will install the jBPM runtime:
ant install.jBPM.runtime
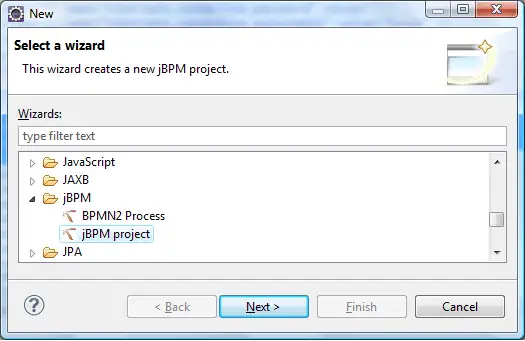
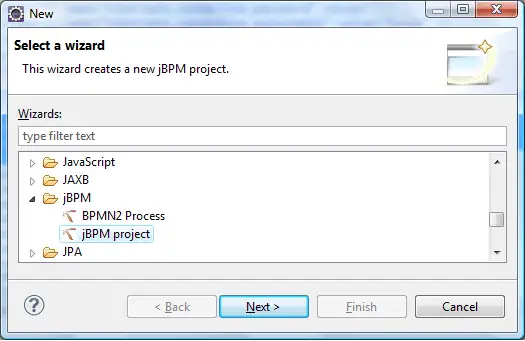
Creating your first jBPM 5 project:
Good, that's all to get started. Now start Eclipse and create a
new jBPM project:
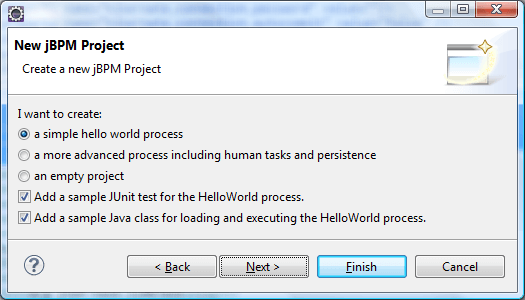
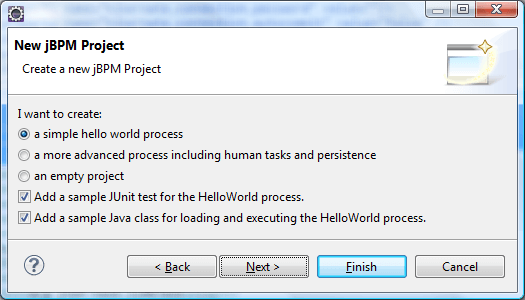
In
this tutorial we will see a basic hello world process, (in the next one
e will show how to deal with of human tasks and data persistence).
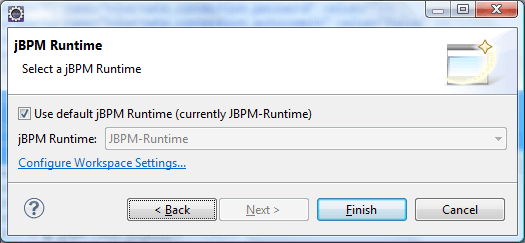
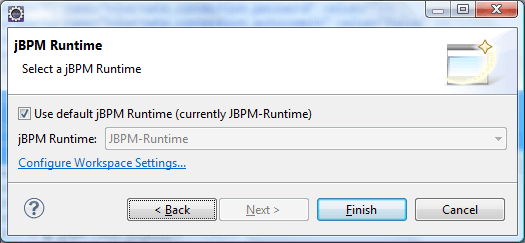
Next you need to specify where your jBPM runtime environment has been
installed (If you have unpacked the jbpm-installer in C:\ it will be
C:\jbpm-installer\runtime)
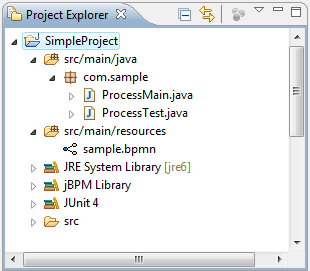
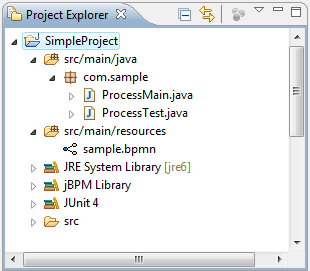
Ok. Now Eclipse shows your first jBPM5 project which contains barely:
- A ProcessMain class which creates and starts a process bound to the sample.bpmn file
- A ProcessTest which can be used for unit testing the ProcessMain class
- A sample.bpmn resource which is our first process written in BPMN 2.0
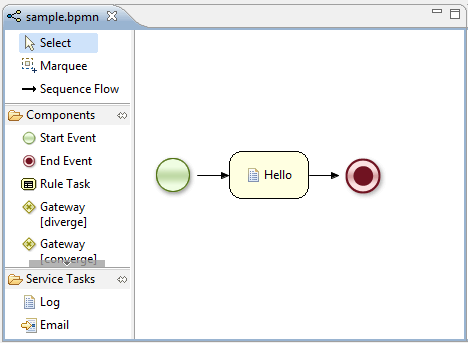
By clicking on the
sample.bpmn file, the BPMN 2 process editor will be activated:
As you can see this process contains a start node, an end node and a
Script task named "Hello".
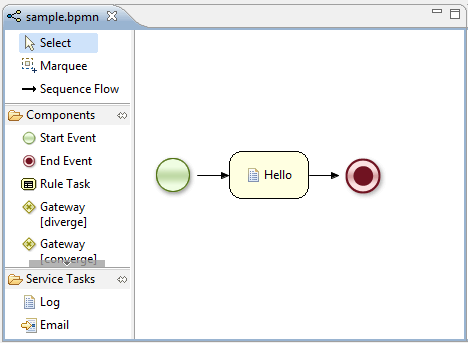 A
Script Task represents a script that should be executed in this
process. The associated action specifies what should be executed, the
dialect used for coding the action (i.e., Java or MVEL), and the actual
action code. This code can access any variables and globals. When a
Script Task is reached in the process, it will execute the action and
then continue with the next node.
A
Script Task represents a script that should be executed in this
process. The associated action specifies what should be executed, the
dialect used for coding the action (i.e., Java or MVEL), and the actual
action code. This code can access any variables and globals. When a
Script Task is reached in the process, it will execute the action and
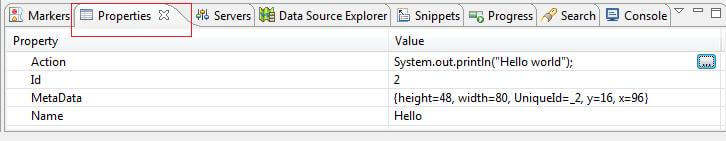
then continue with the next node.By clicking on the "
Properties" tab, in the lower part of your IDE, you can see the Action which is associated to the process.
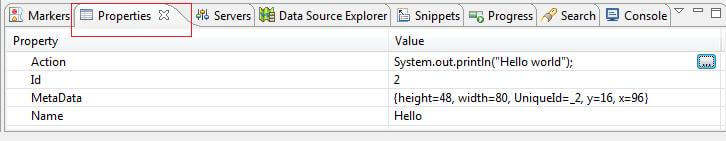
As it is, when you run the ProcessMain, a simple "
Hello world" message will display on the console.
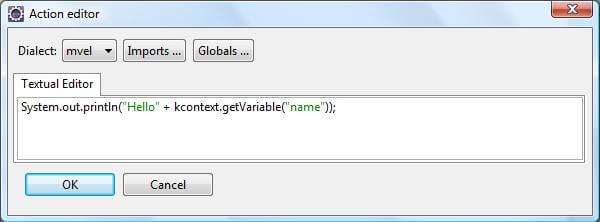
Let's make it a bit more interesting: Right click on the "
Action"
of your node, where the [..] button is displayed. This will let you
redefine your action. Specify the following action in the Textual
editor:
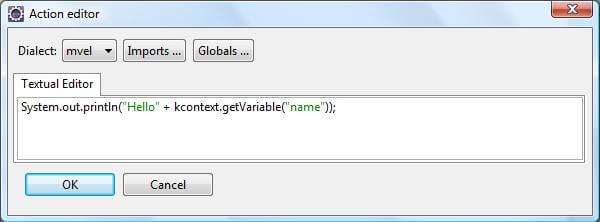 The predefined variable kcontext references the ProcessContext object
(which can, for example, be used to access the current ProcessInstance
or NodeInstance, and to get and set variables, or get access to the
ksession using kcontext.getKnowledgeRuntime()
The predefined variable kcontext references the ProcessContext object
(which can, for example, be used to access the current ProcessInstance
or NodeInstance, and to get and set variables, or get access to the
ksession using kcontext.getKnowledgeRuntime()Now modify your
ProcessMain class, so that the process is started with an HashMap containing the process variables initial value:
01.public class ProcessMain {
02.
03.public static final void main(String[] args) throws Exception {
04.
05.KnowledgeBase kbase = readKnowledgeBase();
06.StatefulKnowledgeSession ksession = kbase.newStatefulKnowledgeSession();
07.
08.Map params = new HashMap();
09.
10.params.put("name", "Arthur");
11.
12.
13.ksession.startProcess("com.sample.bpmn.hello",params);
14.}
15.
16.private static KnowledgeBase readKnowledgeBase() throws Exception {
17.KnowledgeBuilder kbuilder = KnowledgeBuilderFactory.newKnowledgeBuilder();
18.kbuilder.add(ResourceFactory.newClassPathResource("sample.bpmn"), ResourceType.BPMN2);
19.return kbuilder.newKnowledgeBase();
20.}
21.
22.}
Ok,
we have just instructed jBPM to start a process and into the Script
task, to display the "name" process variable. Verify it by running the
ProcessMain class.